CyberSploit1 OffSec Walkthrough: Today we are going to solve another boot2root challenge called “CyberSploit: 1”. It’s available at Vulnhub and OffSec for penetration testing. This is an easy level lab. The credit for making this lab goes to cybersploit1. Let’s get started and learn how to successfully break it down.
Level: Easy
Penetration Testing Methodology
Reconnaissance
- Nmap
Enumeration
- Gobuster
Exploiting
- Basic Cryptography
- CyberChef
Privilege Escalation
- Local Privilege Escalation ‘Overlays’
- Capture the flag
Walkthrough
Reconnaissance
So, let’s start by listing all the TCP ports with nmap.
nmap –sV -sC -p- 192.168.10.190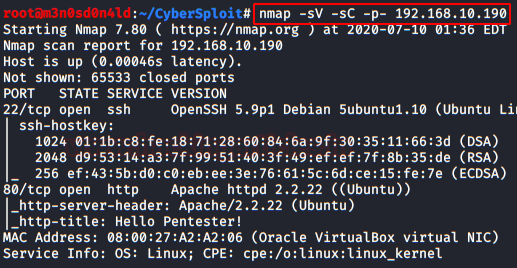
To work more comfortably, I’ll put the IP address in /etc/hosts.

Enumeration
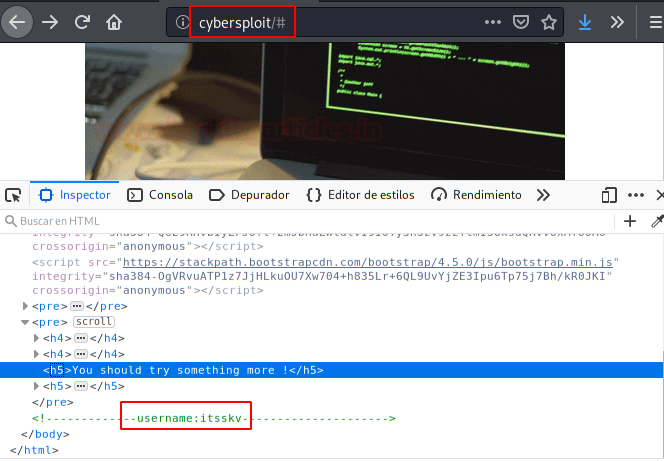
We access the web service and review the source code. We find the SSH user name.
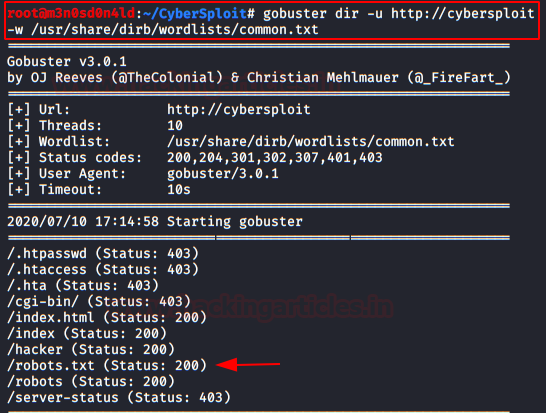
It’s time to fuzzing! We used Gobuster and found several files. We examined the robots.txt and found a base64 text.
Exploiting
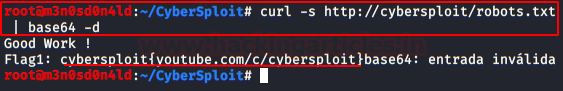
We use curl and add “base64 -d” to the command to decode the message in plain text. We get the first flag, the flag is the user’s password “itsskv“.
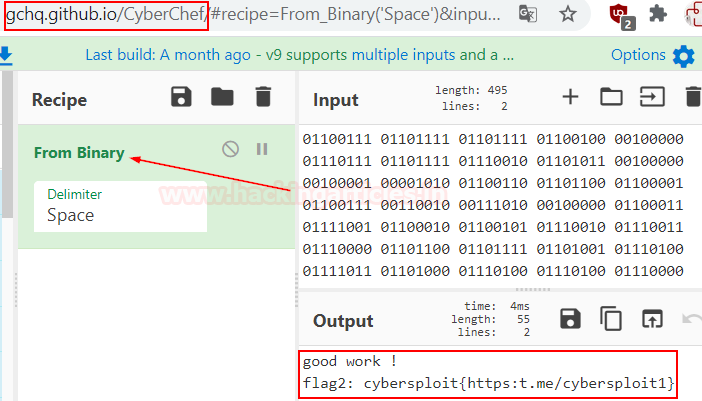
We access with the obtained credentials and read the file “flag2.txt“. Inside, we find a new code, this time it’s “binary code“.

We use the online tool “Cyberchef” and we get the second flag.
Privilege Escalation (root)
The root is quite simple (as the creator of the machine said it was easy level). The machine has a kernel vulnerable to “overlayfs: Local Privilege Escalation“. We download the exploit, compile it on the victim machine and run it. We get a root prompt and read our flag.

Finally this lab solve see you on next lab 😉
Also Read | Moneybox OffSec Walkthrough











